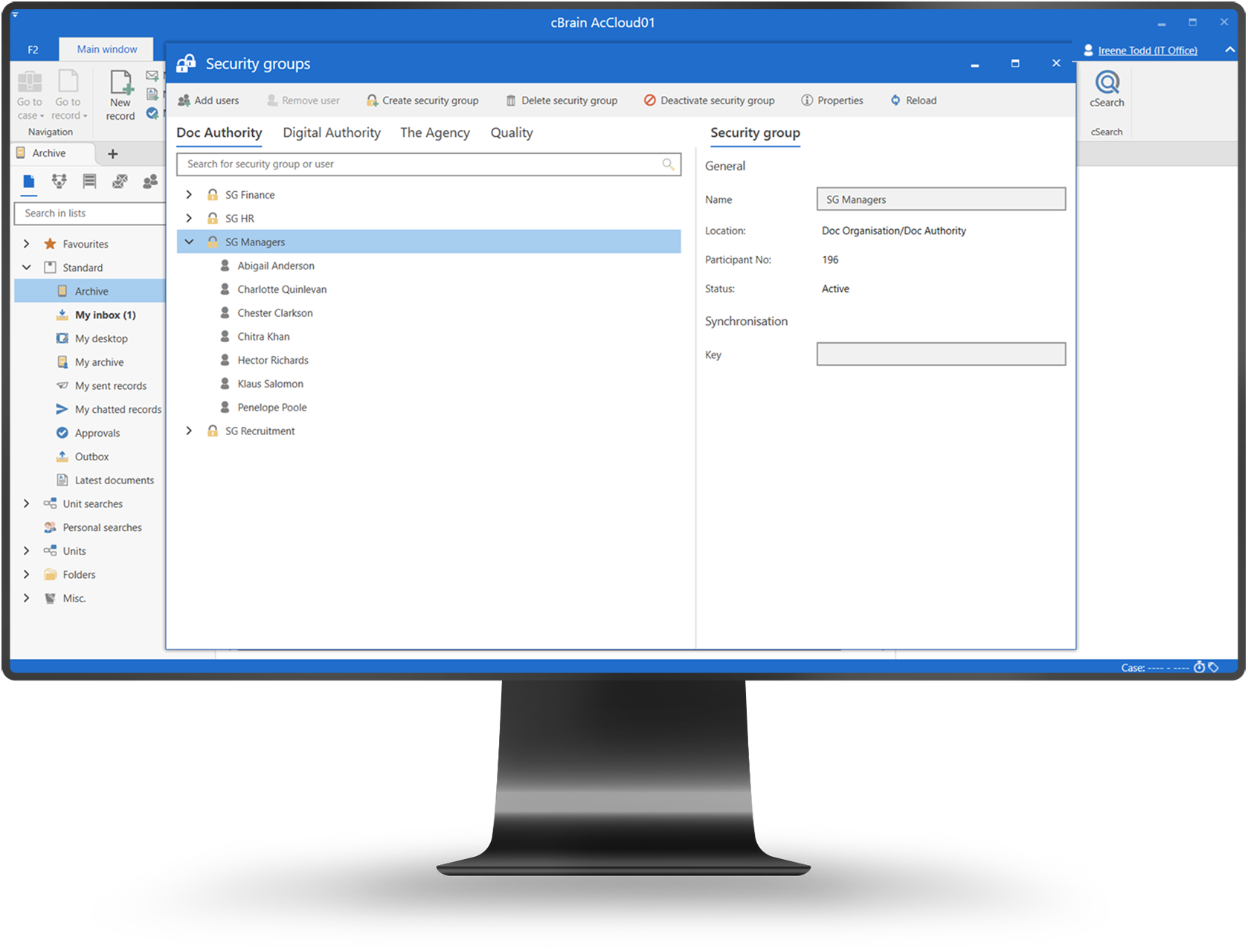

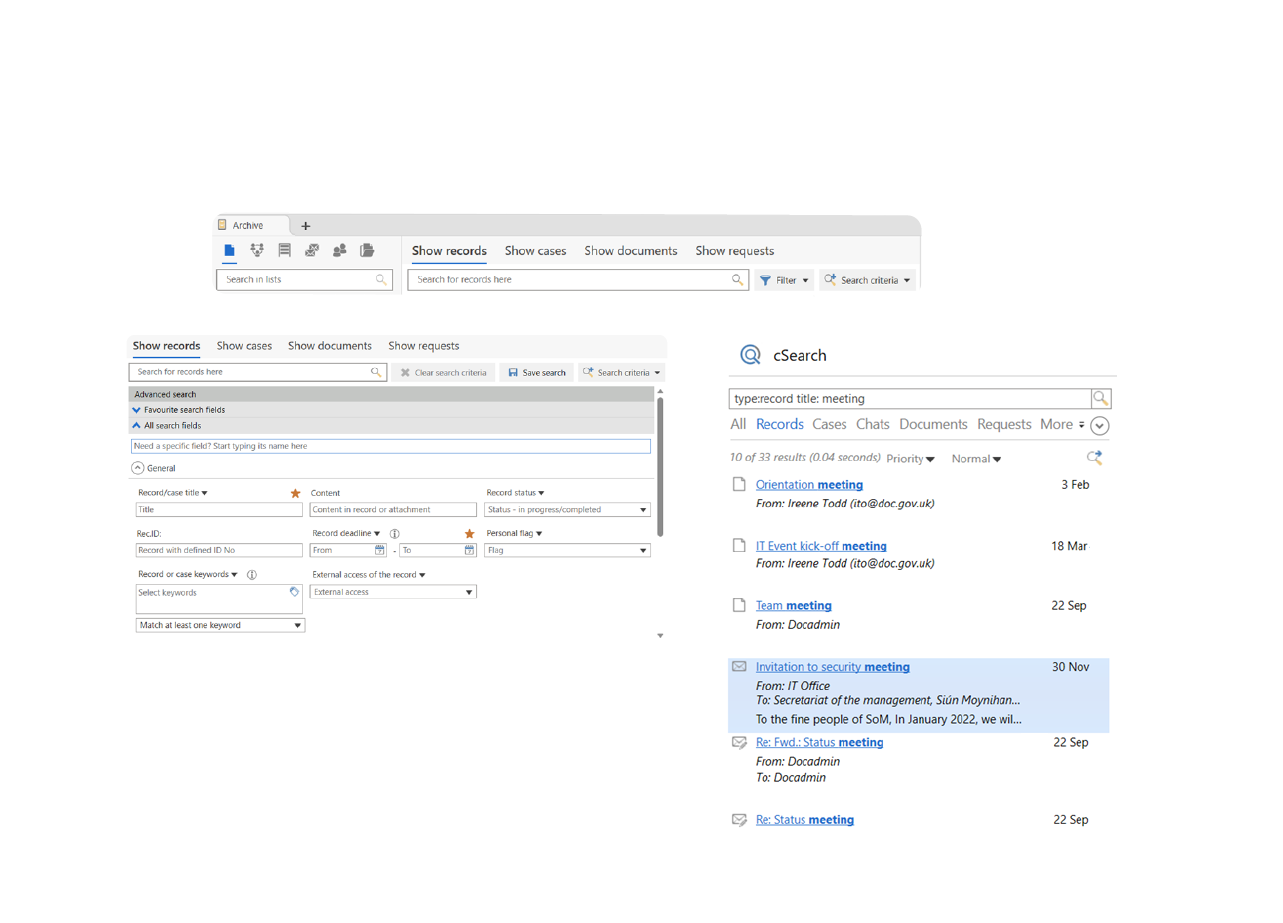
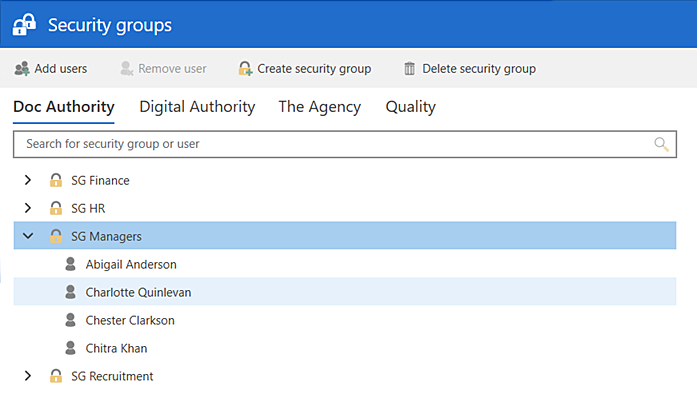
Security groups simplify access management by allowing permissions to be assigned and maintained for groups of users rather than individuals.
Simplified management. Assign access through groups, not individuals.
Consistent rights. Ensure equal access for equal roles.
Scalable control. Manage access efficiently at scale.
Group-based access management
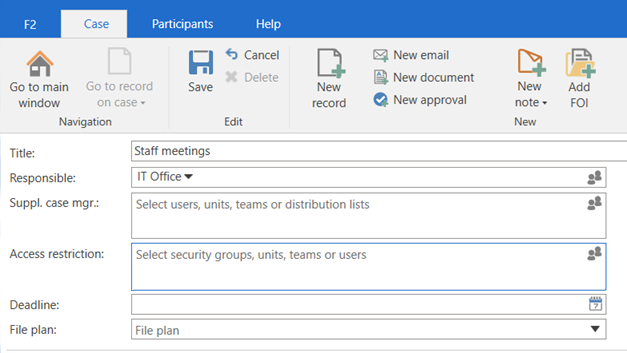
Grant correct access quickly to new staff.
Adapt access as teams and roles change.
Manage access efficiently at scale.
Groups and permissions are managed centrally.
Groups reflect formal organizational roles.
Group changes and assignments are logged.