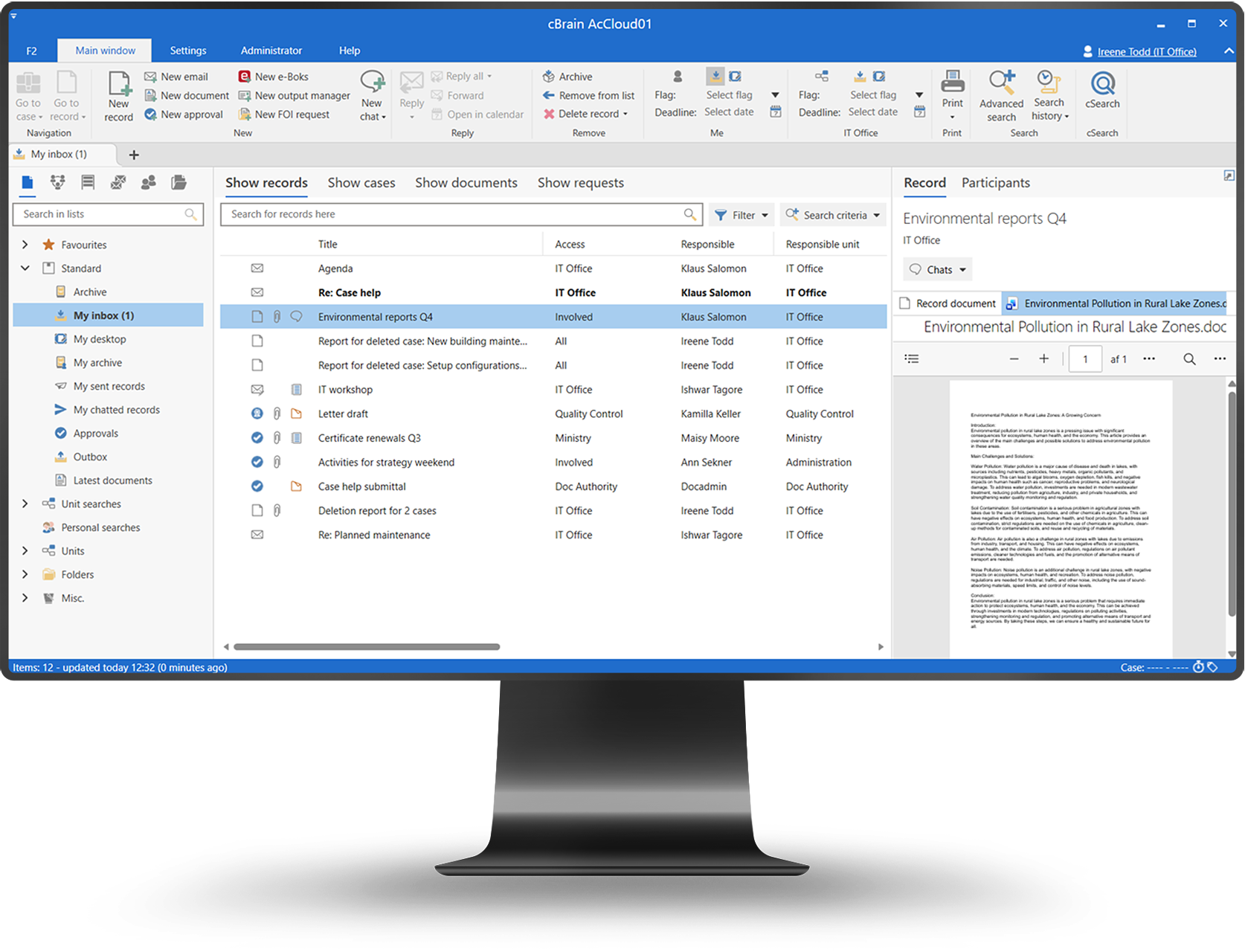

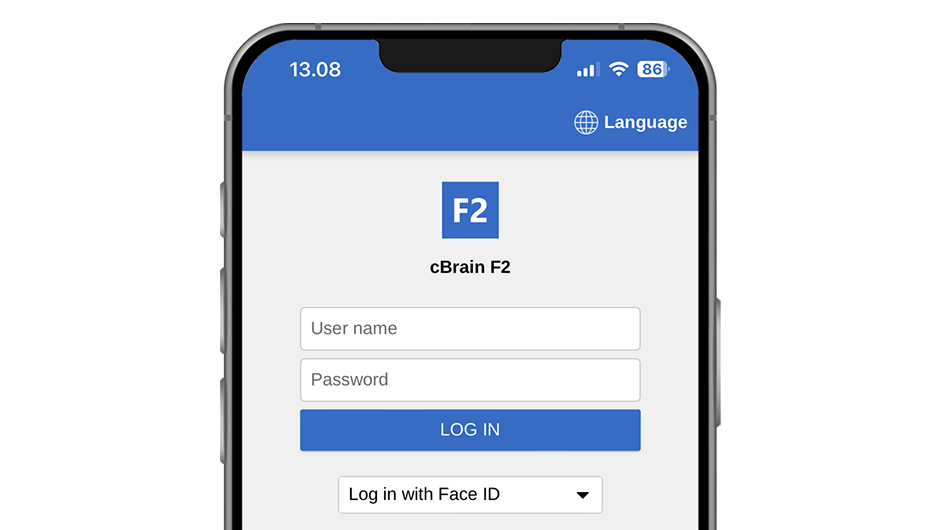
Access control ensures that users only see and act on what they are authorized to — whether working in the office or approving and reviewing work via F2 Manager and F2 Touch.
Secure everywhere. Enforce access across desktop and mobile.
Role-based rules. Apply the same permissions consistently.
Reduced risk. Prevent unauthorized access and actions.
Role-based access management
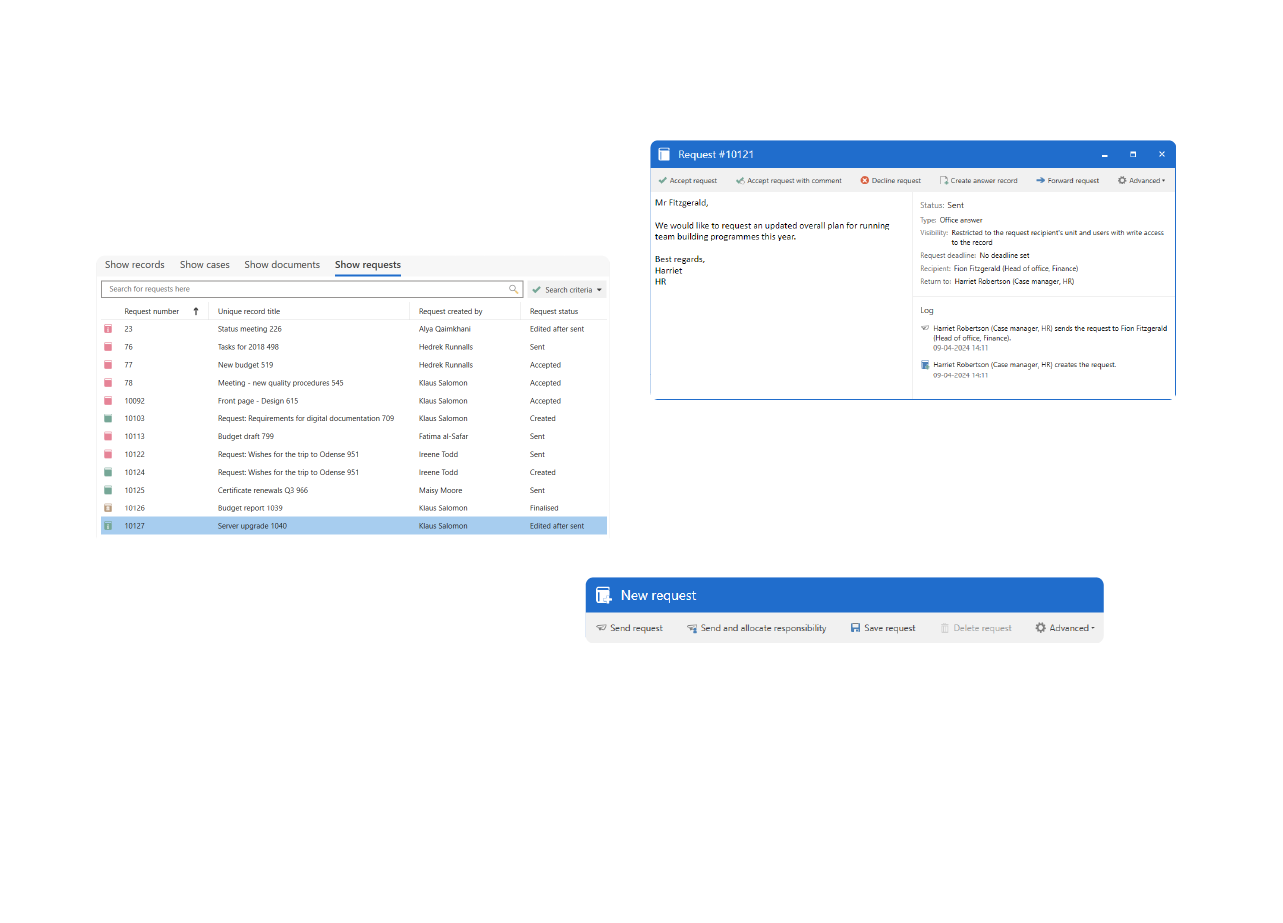
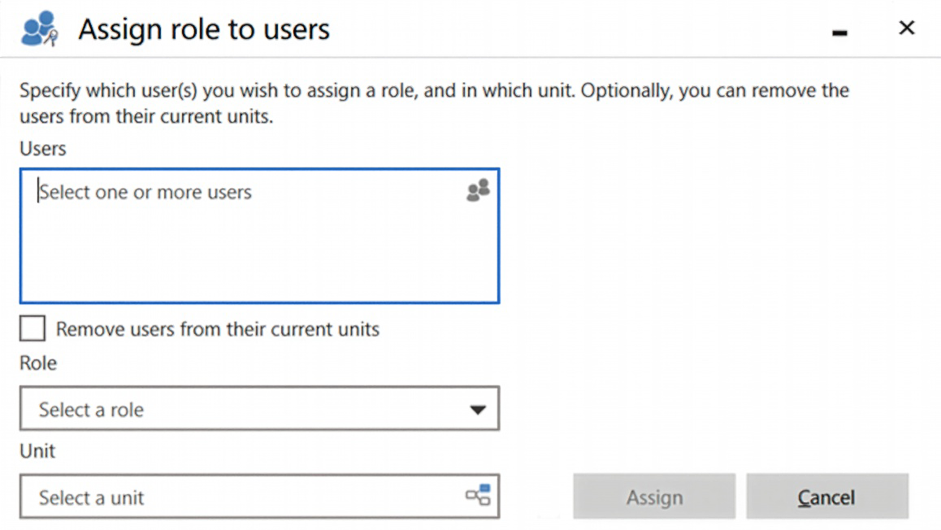
Access rights are defined centrally and enforced consistently, whether users work in the browser, F2 Manager, or F2 Touch.
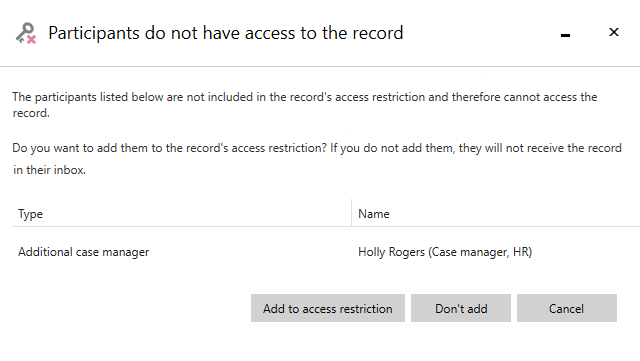
Access to a record is determined by the combination of access level and access restrictions, which together define who can view the record.

Support secure decision-making on the go.
Enable safe access across locations and devices.
Protect confidential information consistently.
Only authorized users can view or act on data.
Access requires authenticated and approved identities.
Access-related actions are logged and traceable.