
Access rights ensure that responsibilities and permissions are clearly defined, enforced consistently, and aligned with organizational roles and policies.
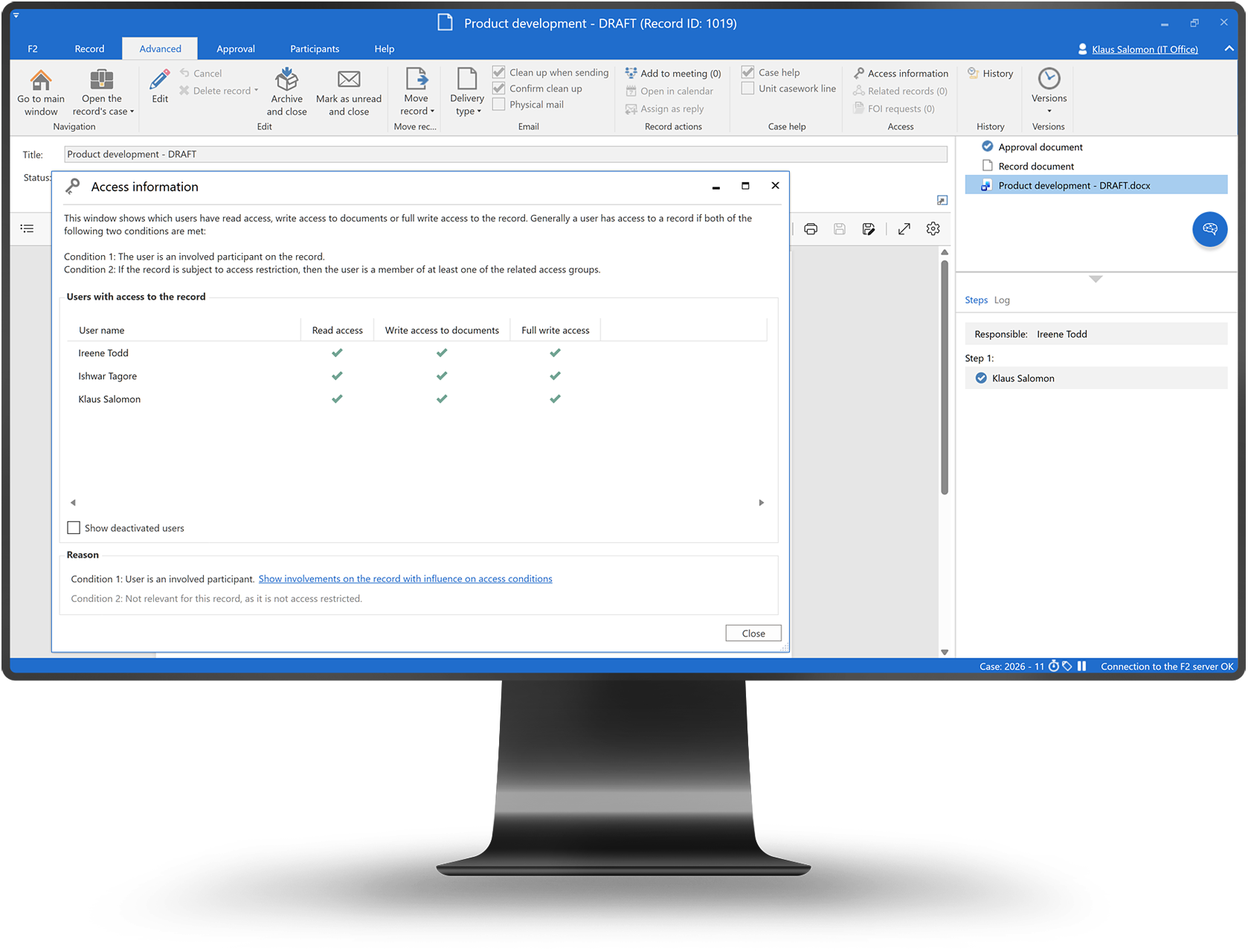
Clear permissions. Define who can view, edit, and approve.
Immediate effect. Apply changes instantly.
Audit support. Log access changes and usage.
Granular permission management
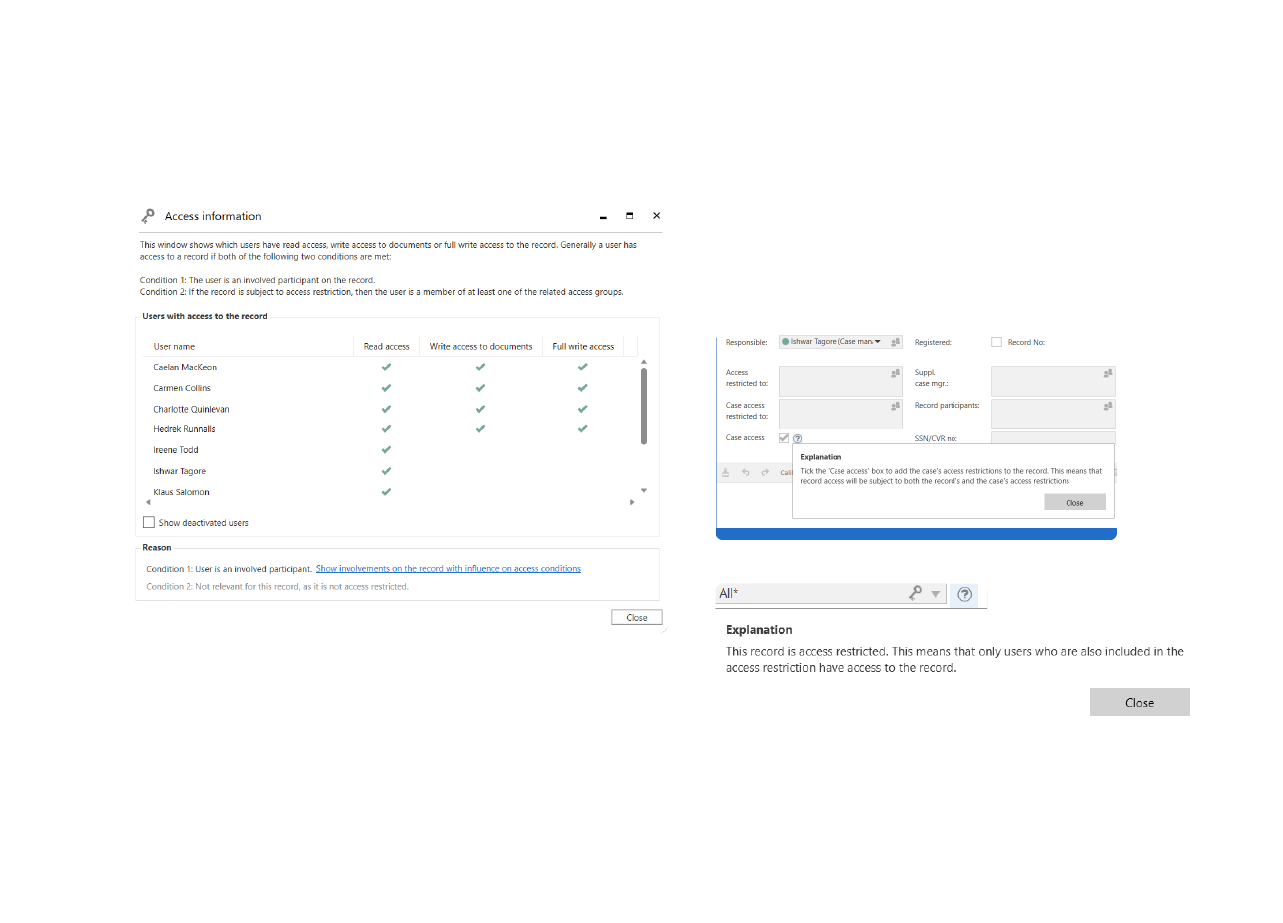
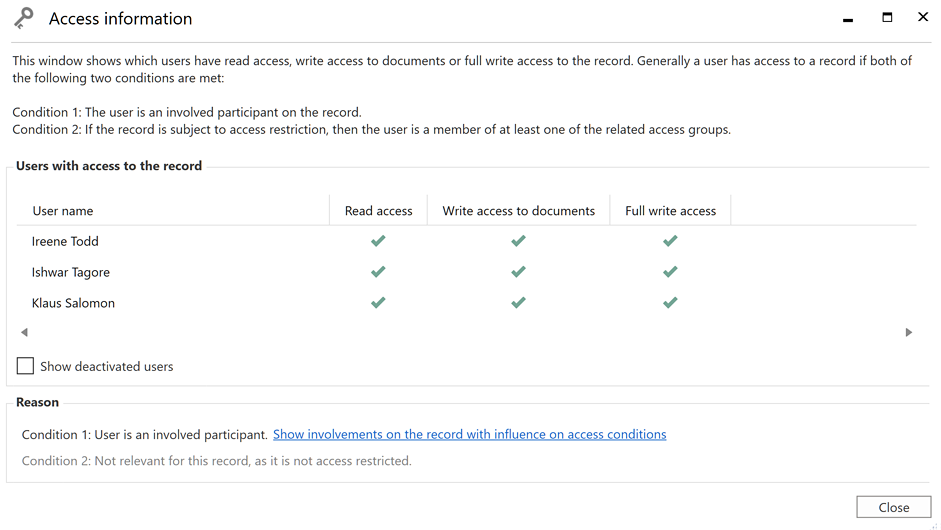
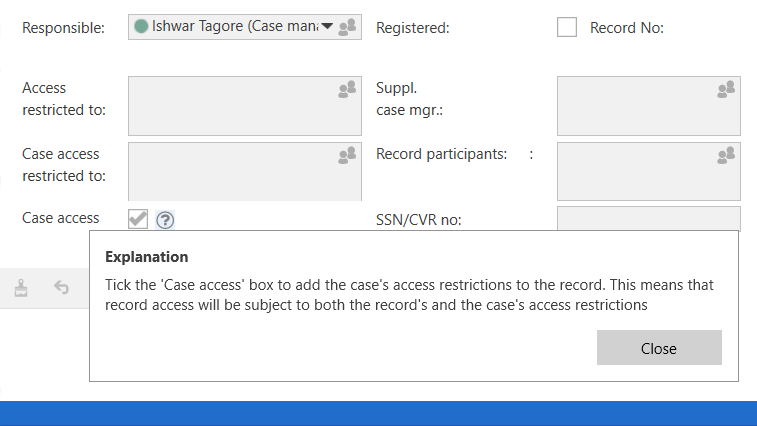
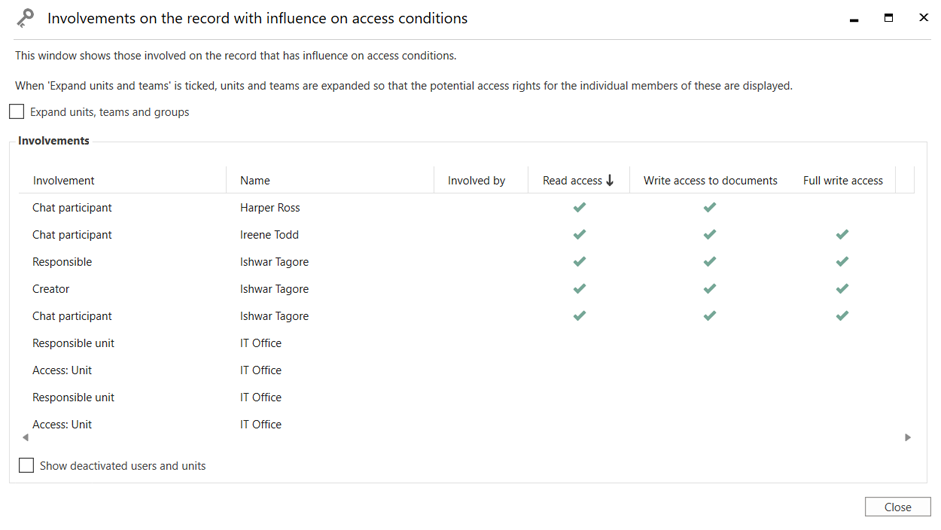
Restrict access to confidential work.
Ensure only authorized roles can approve actions.
Adapt permissions as roles and structures evolve.
Permissions are granted through approved roles only.
Changes apply instantly across the platform.
Access changes and usage are logged and traceable.