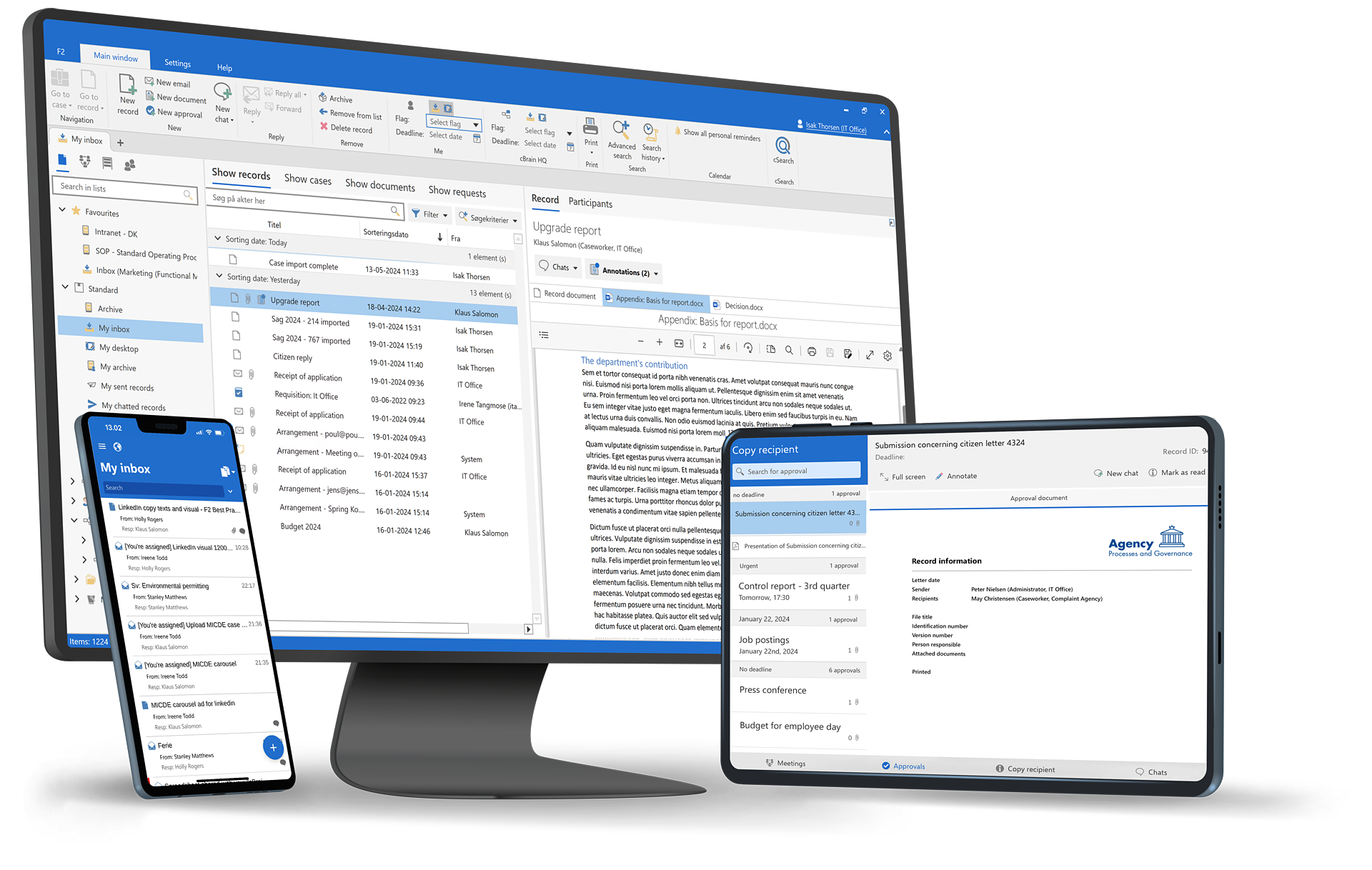

System configuration enables organizations to adapt cBrain F2 to their operational needs through governed, centralized configuration — without custom development. The configuration can be done by the organization's own system administrators, reducing the dependency on cBrain or partners.
Controlled flexibility. Adapt system behavior without code.
Consistent setup. Apply settings organization-wide.
Change discipline. Prevent fragmented configurations.
Central system configuration



Adapt system behavior during restructurings.
Reflect new rules or policies quickly.
Fine-tune system behavior as needs evolve.
Only authorized roles can change system configuration.
All configuration changes are logged and auditable.
Configuration changes follow platform security controls.